Find out how to protect critical infrastructure when an employee leaves. We break down real-world scenarios of password blackmail and technical defense methods that make your control over a building or production facility absolute and independent of any specific individual.

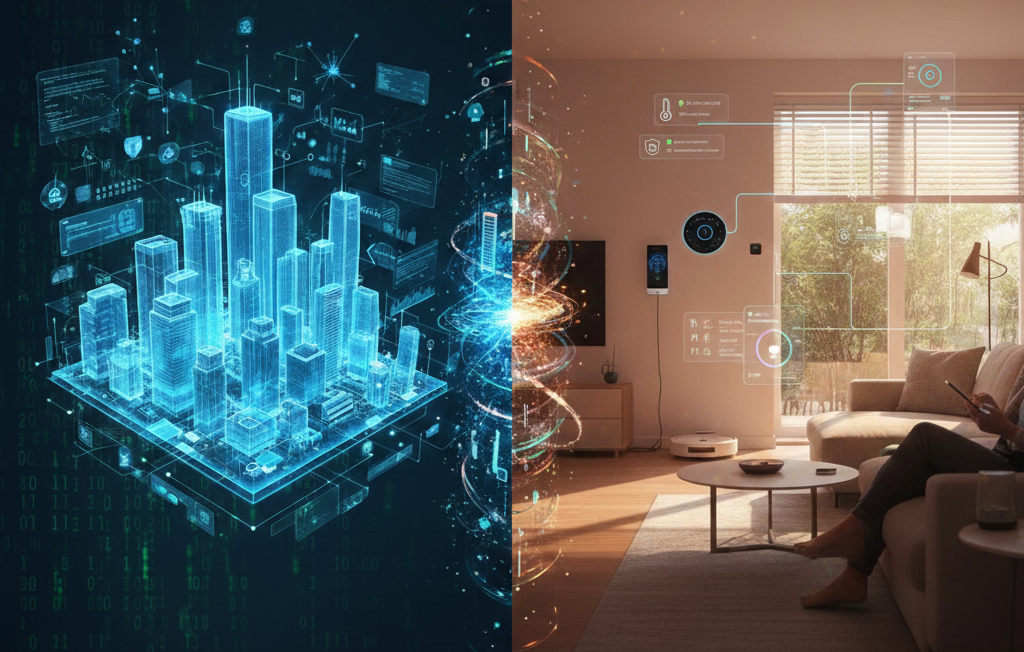
The Illusion of Control
You are confident your facility is protected: expensive controllers are installed, staff is hired, and the server room is under lock and key. But things happen. Real security isn’t about the thickness of the door; it’s about the answer to one question: "Who holds the access keys at 2:00 AM if the head technician stops picking up the phone?"
If access to chillers, ventilation, and IT infrastructure exists only in an employee's head or on a personal drive, you own a concrete box, not the "engineering intelligence" of the building. Loyalty has an expiration date. The human factor isn't a risk—it’s a systemic inevitability.
Case: "The Quiet Departure"
Imagine an engineer who built your system over five years decides to leave. No drama; they just found a better job. A week later, you realize that to change the HVAC schedule or adjust lighting, you need a BMS master password that they "forgot to update in the database." Or worse: the project file remained on their personal laptop.
Suddenly, you are a beggar at your own facility. You call, you plead, you offer money. Meanwhile, the automation begins to glitch. The AC starts chilling in winter, and the heaters decide to "warm up" the building in July. The result: weeks of negotiations and lost revenue just to access your own systems. This happens because the architecture allowed a human to become a "single point of failure."
- Cloud AI & Edge Computing: All configurations and control logic are backed up in a secure cloud. You are the sole owner of the master account. Engineer left? Revoke their access in two clicks. The system won't "forget" passwords; they are always at your fingertips.
- Technological Freedom:Connect any devices using standard Modbus and BACnet protocols. You don't need "that one guy with that specific software" to tweak a temperature setpoint.
- Emotional Freedom: This is vital. With Uspace’s architectural protection, you don't need to harbor suspicion. You can truly trust your team, knowing that your "Digital Twin" insurance guarantees stability under any scenario.
Do You Have Insurance?
The problem isn't "trust." We all trust our employees. But trust is an emotion, while asset management is a technology.
When you insure a warehouse against fire, you don't plan to set it ablaze; you create conditions where an incident doesn't become a catastrophe. Automation is the same. Most classic systems are "black boxes"—keys are easily lost and nearly impossible to recover without the vendor or that specific "guru."
Your system’s security shouldn't depend on staff loyalty; it’s a matter of architectural insurance.
Uspace — Guaranteed Ownership
Uspace is a system where the client's ownership is absolute and technically enforced. We use a Customer First approach to eliminate the possibility of manipulation.
Checklist: "Insurance Audit" (Do this today)
If you checked "No" to even one point, your insurance isn't working.
Don't wait for "things to happen." Confirm control over your facility with action, not just a "pinky promise." Schedule an engineering systems audit with Uspace —we’ll make your automation transparent and immune to the human factor.